CYBER THREAT INTELLIGENCE
Conquering uncertainty and illuminiating the unknown
The Cyber Threat
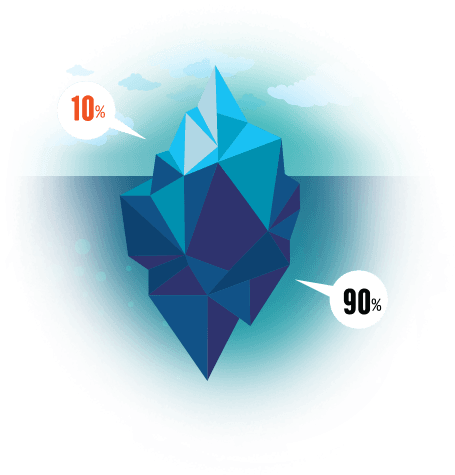
The ‘visible web’ that we commonly term as the internet, is just about 0.1% of the entire World Wide Web. The 99.9% remains hidden from search engines and standard browsers.
This is the enormity of the dark web (or black web) where massive amounts of information, communication and data gets transmitted and transacted in. The scary thing is that all these remains invisible and concealed for most of us.
Dark Activities Hidden from View
- Sharing, transferring and selling of sensitive information which includes credit card and personal identification details, national security information, and more.
- Selling and purchase of banned products such as firearms, weapons, drugs and more.
- Information on the planning of attacks or cyber-attacks on individuals, organisations and government bodies.
- Malware infected devices capable of orchestrating IoT attacks and compromise organisational operations and credibility.
Dark Web Monitoring
Hidden activities in the dark web must be tracked and monitored to fully protect you and your organisation. Our cyber intelligence solution analyses an organisation’s digital shadow of all sizes and will act as an important pre-emptive strike against any possible threats by administering takedowns to ensure that your company is fully protected. In the uncertain world of the dark web, we fight to give you and your organisation the upper hand.
Malware Intelligence

Our Network Intelligence covers over 100 million Infected Hosts. Our huge database also consists of monitoring and tracking down Vulnerable Hosts which include SSL Heartbleed, Shellshock, Juniper Backdoor, Uploaded Web-shells, Malicous FTPs, and many more. We also have a complete Malware Library with access to millions of malware hashes and active Sandboxes.
Read More
DDoS Protection
Multi-layered DDoS Protection capable of mitigating any type of attack on any website.
Multiple scrubbing nodes in New York, Los Angeles, London, Singapore, Vancouver, and Hong Kong.
Read More
Cyber Readiness Platform

Controlled and Realistic Simulated DDoS attack to test the resiliency of your critical infrastructure and effectiveness of your mitigation tools
Read More


